NIAP 4.0 Isolators
Operation of a NIAP PP4.0 secure isolator
Isolators are hardware devices designed to ensure an unidirectional separation between a computer and its peripherals (monitor, keyboard, mouse).
They prevent any information leakage, even in the event of a software or physical attack.
They ensure:
- A strictly unidirectional video flow: computer → monitor
- A strictly unidirectional keyboard/mouse flow: peripherals → computer
- No opposing flow is possible, even if the equipment is compromised.

General architecture of a NIAP PP4.0 secure isolator
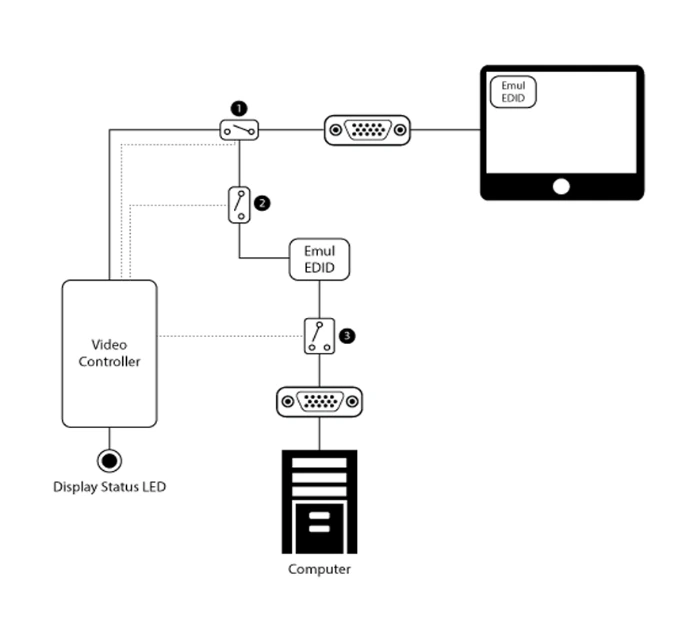
The architecture of the isolator is based on a complete physical separation between the computer and its peripherals. A dedicated system controller drives the whole system, loads firmware into non-modifiable memory, and performs self-tests at startup to ensure the integrity of the device.
Keyboard and mouse signals pass through USB emulators that verify the peripherals are authorized, then are transmitted through optical diodes, creating a strictly unidirectional flow to the computer, with no possibility of return or reverse manipulation.
The video path is designed on the same principle: the signal goes from the PC to the monitor only, while a Emulated EDID completely protects the display configuration channel by blocking any attempt to write or exploit it by the computer.
Finally, the whole is protected in a tamper-proof chassis welded, accompanied by holographic seals that allow detection of any unauthorized opening attempts.
NIAP PP4.0 secure isolators High Secure Labs
The NIAP PP4.0 HSL secure isolators provide a unidirectional material protection designed for the most sensitive environments. They prevent any information leakage between secure systems and peripherals — video, audio, and USB only flow in one direction.
Thanks to their enhanced EDID control and isolation, they protect classified workstations against attacks coming through projectors, screens, or uncontrolled accessories.
These solutions, certified NIAP Common Criteria PP4.0, meet the strict requirements ofarmed forces, government agencies, and critical infrastructures.
